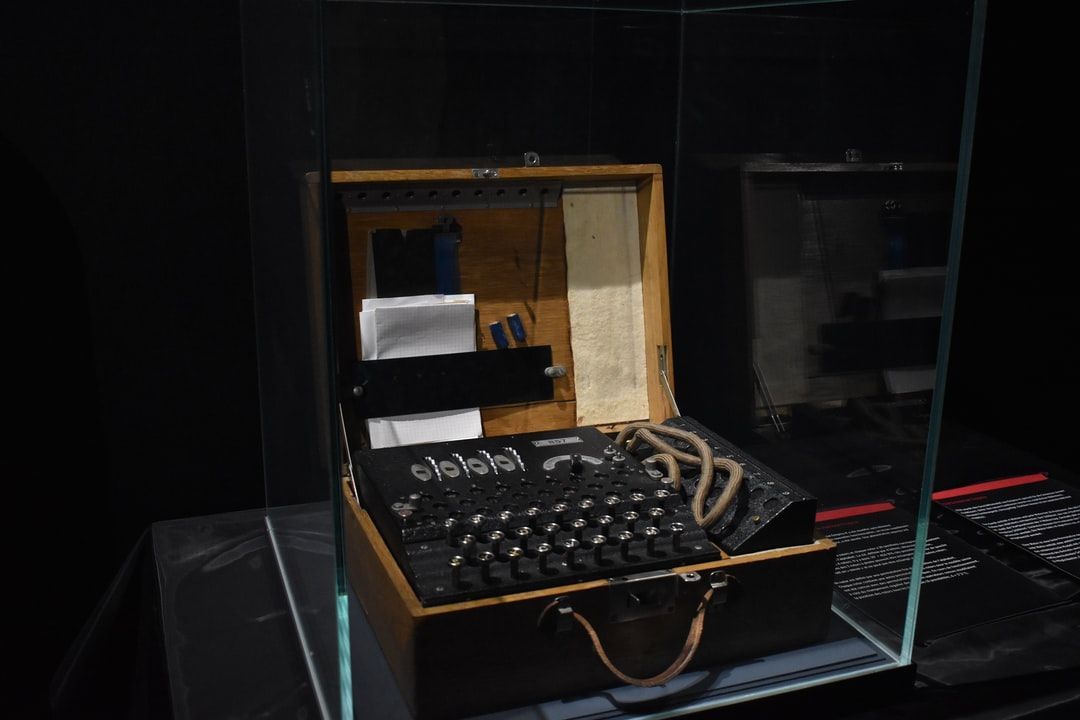
The art and science of encrypting your messages before sending them out. From Hitler's Enigma to your Whatsapp messages, cryptography has seen it all.
 Imagine, you are messaging your business partner about a super secret idea, it is worth $ 1m, will you trust the messaging application not to read your super secret conversation? No, right. No one will, still people across the world use whatsapp for such sensitive messaging (although I prefer telegram for my secret conversations). Well, turns out, it is because most messaging apps(including whatsapp) use a technique called End to End Encryption, which doesn’t allow these messaging services or their employees to read your conversations with your contacts. But how does this works, well, that is what we will try to understand here.
Imagine, you are messaging your business partner about a super secret idea, it is worth $ 1m, will you trust the messaging application not to read your super secret conversation? No, right. No one will, still people across the world use whatsapp for such sensitive messaging (although I prefer telegram for my secret conversations). Well, turns out, it is because most messaging apps(including whatsapp) use a technique called End to End Encryption, which doesn’t allow these messaging services or their employees to read your conversations with your contacts. But how does this works, well, that is what we will try to understand here.
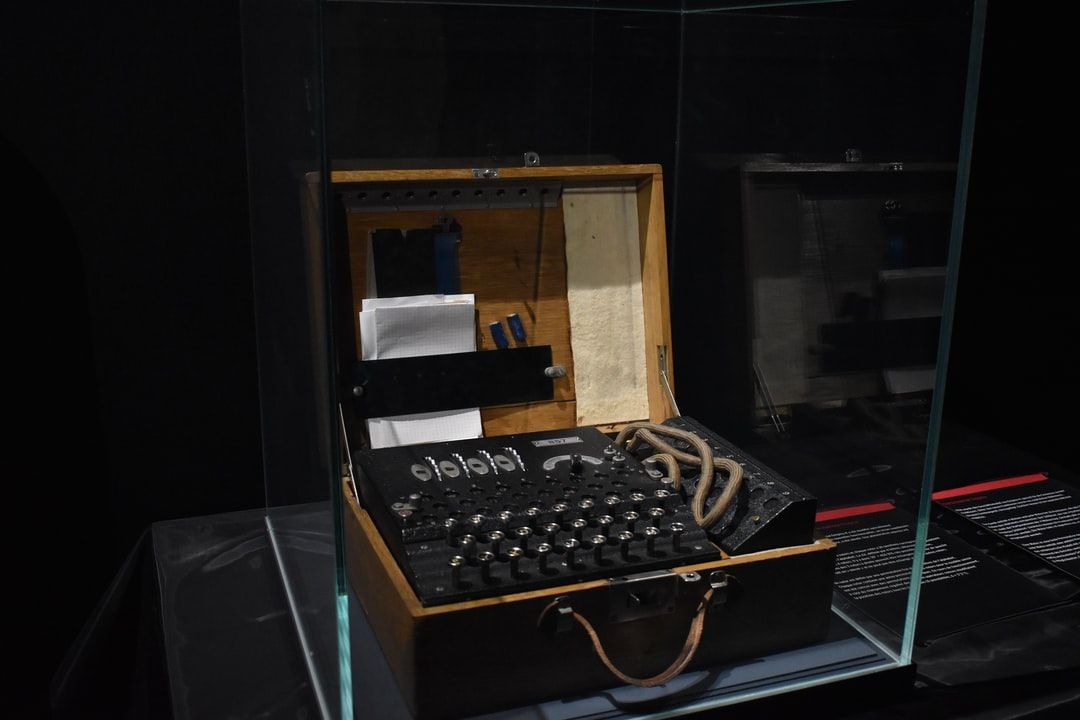
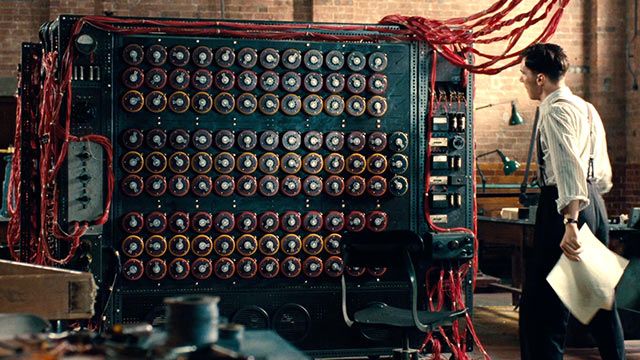 Many new developers are jumping right into coding (usually for those fat paychecks) without learning much about the history of Computer Science. People regarded Alan Turing as the father of Computer Science. He was first a cryptologist and mathematician. Then, he pioneered the field of CS in order to solve cryptological problems.
Many new developers are jumping right into coding (usually for those fat paychecks) without learning much about the history of Computer Science. People regarded Alan Turing as the father of Computer Science. He was first a cryptologist and mathematician. Then, he pioneered the field of CS in order to solve cryptological problems.
 Quantum Computing
Quantum Computing
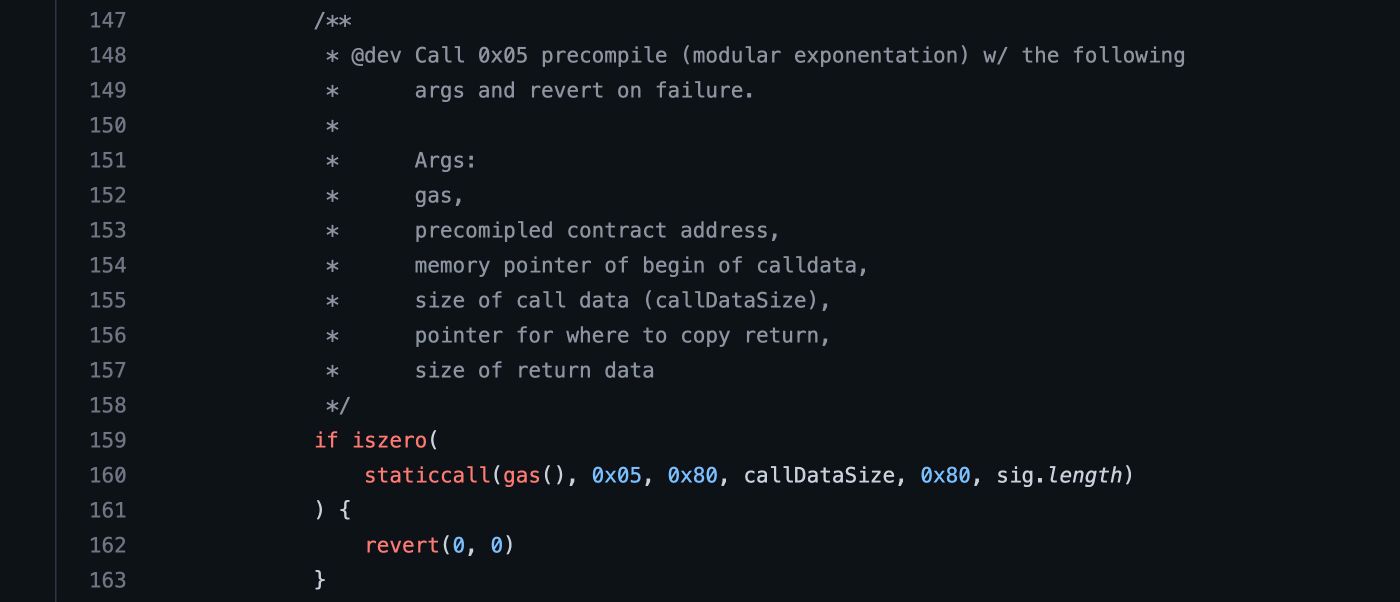
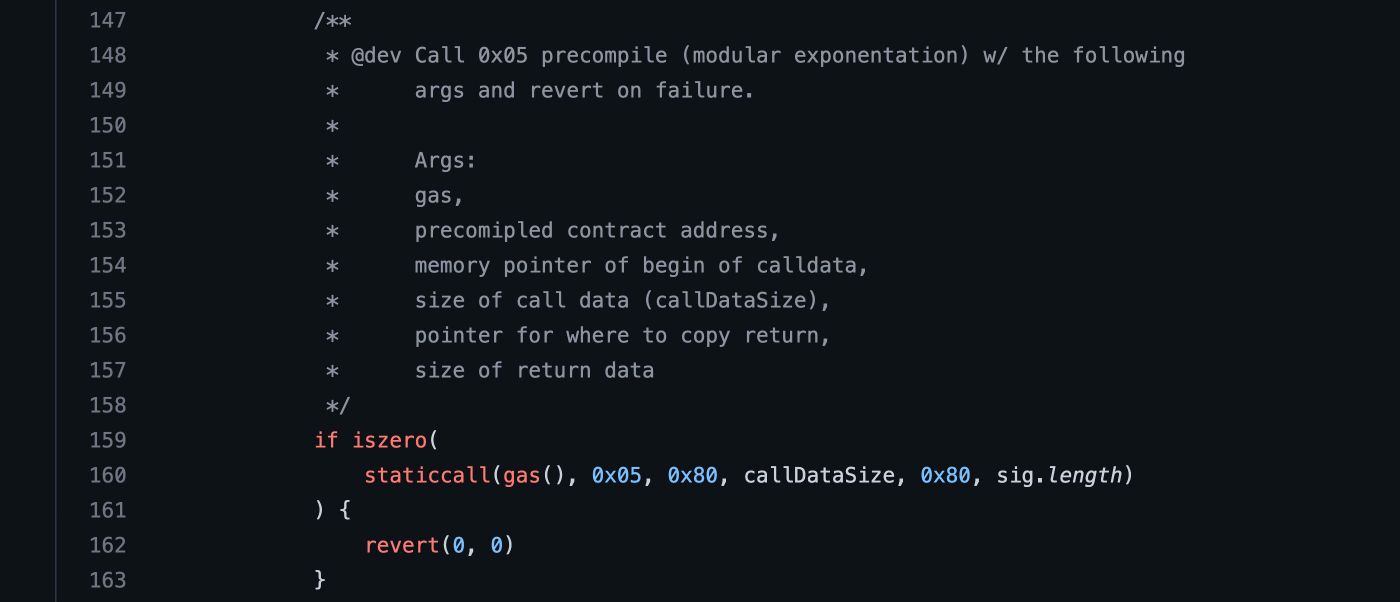
 Among all popular polynomial commitment schemes, KZG is the best scheme in terms of succinctness but triggers security concerns.
Among all popular polynomial commitment schemes, KZG is the best scheme in terms of succinctness but triggers security concerns.
 Bitcoin improvement proposal 32 is, in my opinion, one of the most important BIPs we have. (Thanks Peter Wuille!) BIP 32 gave us Hierarchical Deterministic Wallets. That is, the ability to create a tree of keys from a single seed.
Bitcoin improvement proposal 32 is, in my opinion, one of the most important BIPs we have. (Thanks Peter Wuille!) BIP 32 gave us Hierarchical Deterministic Wallets. That is, the ability to create a tree of keys from a single seed.
 One of the main reasons that lead to insecure NodeJS applications is insecure or bad usage of cryptography APIs. Developers who are not very familiar with such APIs and the underlying crypto concepts often struggle to choose secure configuration options or to even get their code up and running.
One of the main reasons that lead to insecure NodeJS applications is insecure or bad usage of cryptography APIs. Developers who are not very familiar with such APIs and the underlying crypto concepts often struggle to choose secure configuration options or to even get their code up and running.
 Today, we are gonna learn how to apply coding skills to cryptography, by performing image-based stenography which hiding involves secret messages in an image.
Today, we are gonna learn how to apply coding skills to cryptography, by performing image-based stenography which hiding involves secret messages in an image.
Stenography has been used for quite a while. Since World War II, it was heavily used for communication among allies so as to prevent the info being captured by enemies
 If you care about your security on the web, you probably use a Two-Factor authentication (2FA) method to protect your accounts. There are various 2FA methods available out there, a combination of password + fingerprint, for example, is one of them. However, since not so many people have a fingerprint reader available all the time, one of the most popular 2FA methods today is to use an authenticator app on your cellphone to generate a temporary password that expires within a minute or even less. But, how does this temporary password, called Time-Based One-Time Password (TOTP) works, and how can I implement that on my own service?
If you care about your security on the web, you probably use a Two-Factor authentication (2FA) method to protect your accounts. There are various 2FA methods available out there, a combination of password + fingerprint, for example, is one of them. However, since not so many people have a fingerprint reader available all the time, one of the most popular 2FA methods today is to use an authenticator app on your cellphone to generate a temporary password that expires within a minute or even less. But, how does this temporary password, called Time-Based One-Time Password (TOTP) works, and how can I implement that on my own service?
 This article talks about quantum computing and why it can break encryption in blockchains such as Bitcoin and Ethereum.
This article talks about quantum computing and why it can break encryption in blockchains such as Bitcoin and Ethereum.
 The particular challenge I'm speaking of is cleverly called Krypton, because it’s a crypto challenge, on the main page you are given hints and examples.
The particular challenge I'm speaking of is cleverly called Krypton, because it’s a crypto challenge, on the main page you are given hints and examples.
 Imagine if any kind of blockchain you are currently looking at is a 2D point of view of a 3D shaped blockchain. If you want to discover more read my story !
Imagine if any kind of blockchain you are currently looking at is a 2D point of view of a 3D shaped blockchain. If you want to discover more read my story !
 Organizations nowadays are storing and performing computation of the data on the cloud instead of handling themselves. Cloud Service Providers (CSPs) provide these services at an affordable cost and low maintenance. But to ensure compliance and retain privacy, organizations need to transfer the data in an encrypted format, which does ensure the confidentiality of the data. However, once the data reaches the cloud, the CSP has to decrypt the data to perform operation or computation.
Organizations nowadays are storing and performing computation of the data on the cloud instead of handling themselves. Cloud Service Providers (CSPs) provide these services at an affordable cost and low maintenance. But to ensure compliance and retain privacy, organizations need to transfer the data in an encrypted format, which does ensure the confidentiality of the data. However, once the data reaches the cloud, the CSP has to decrypt the data to perform operation or computation.
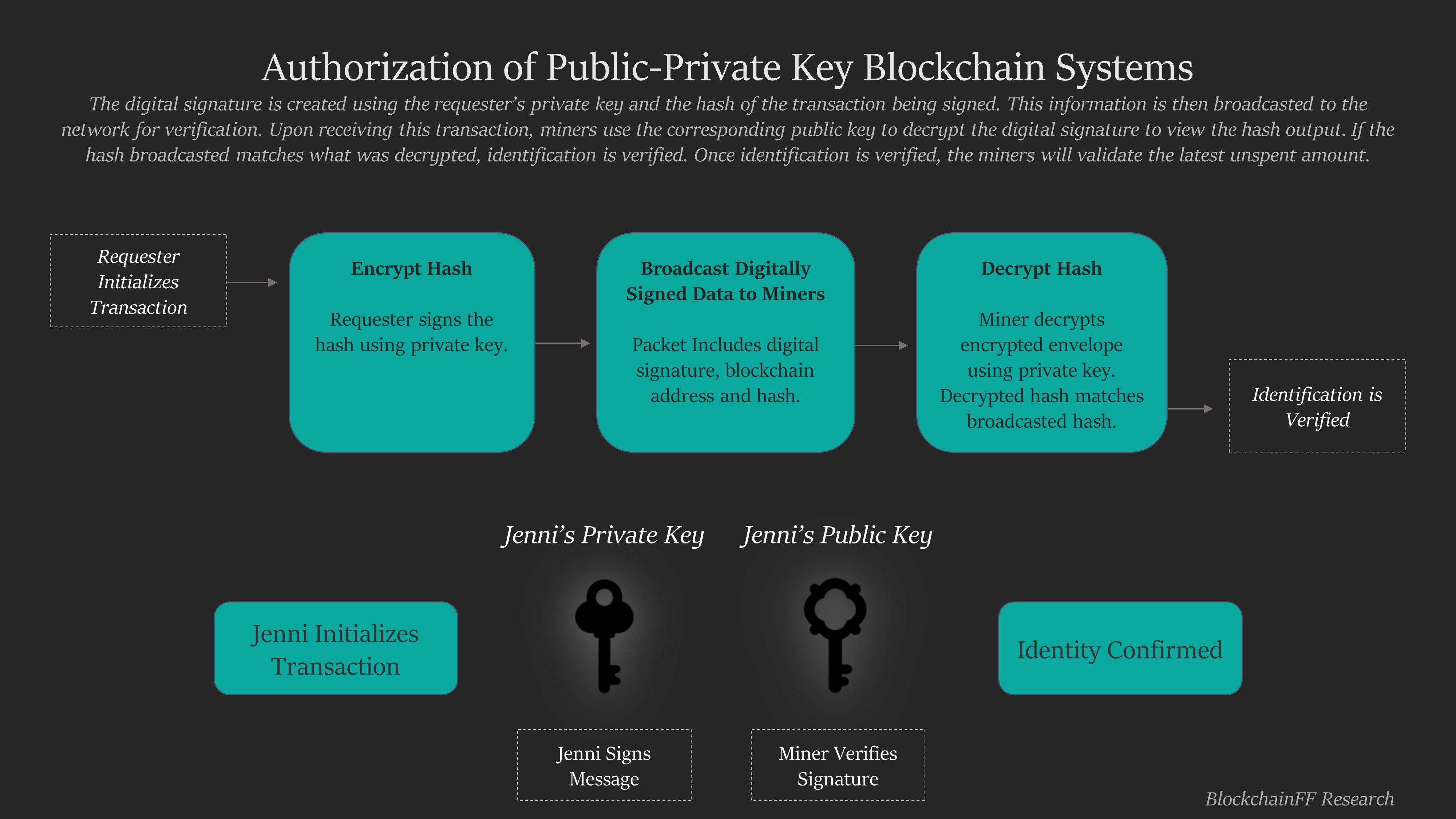
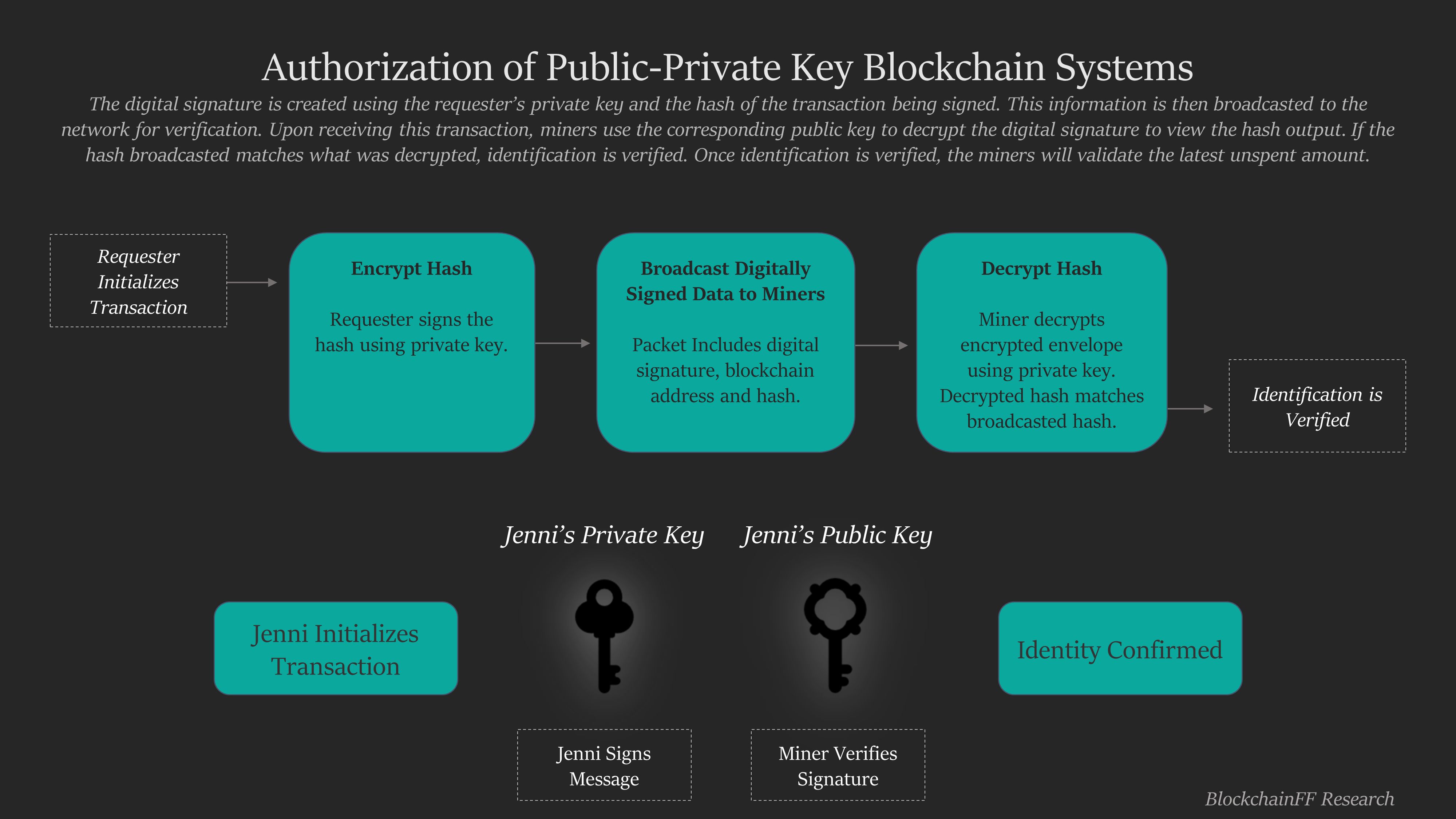
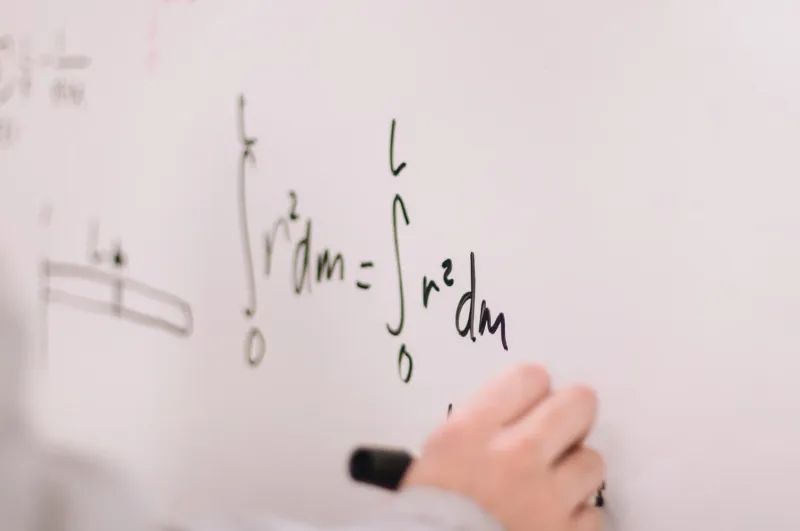
 Cryptography makes Blockchain Technology more robust and stands out from other technology. Cryptography which uses advance mathematical principles method in transmitting and storing the data, it stores in a way that only the person for whom the data is intended can read and process it.
Cryptography makes Blockchain Technology more robust and stands out from other technology. Cryptography which uses advance mathematical principles method in transmitting and storing the data, it stores in a way that only the person for whom the data is intended can read and process it.
 If you are going deep into cloud security you may have seen the term “Envelope encryption”. Let’s explain the concept and why it is useful.
If you are going deep into cloud security you may have seen the term “Envelope encryption”. Let’s explain the concept and why it is useful.
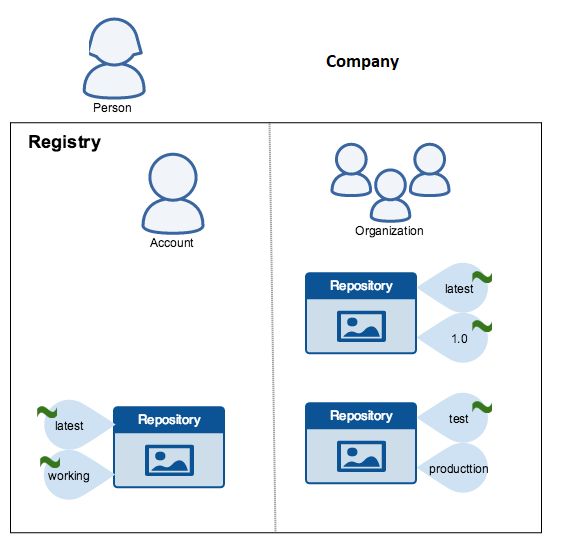
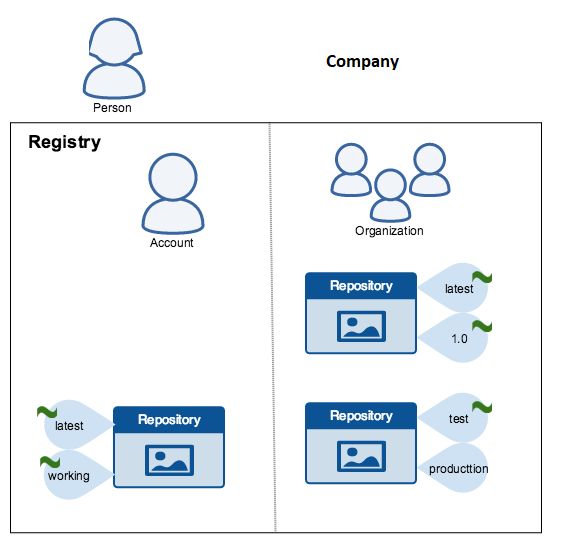 Strong cryptographic assurances are needed to secure data. This is where Docker Content Trust (DCT) comes into the picture.
Strong cryptographic assurances are needed to secure data. This is where Docker Content Trust (DCT) comes into the picture.
 A look at updated encryption standards based on strides in quantum cryptography.
A look at updated encryption standards based on strides in quantum cryptography.
 Let’s explain exactly what that term means in one sentence:
Let’s explain exactly what that term means in one sentence:
 The reason XOR is so special in cryptography
The reason XOR is so special in cryptography
 Startup interview with Antoni Zolciak of Aleph Zero, a public blockchain with enhanced privacy features. We combine academic excellence with business know-how.
Startup interview with Antoni Zolciak of Aleph Zero, a public blockchain with enhanced privacy features. We combine academic excellence with business know-how.
 Garbled circuits are a quite old, and surprisingly simple, cryptographic primitive and simplest form of general-purpose MPC to wrap your head around.
Garbled circuits are a quite old, and surprisingly simple, cryptographic primitive and simplest form of general-purpose MPC to wrap your head around.
 Currently, Bitcoin is quite limited in regards to its cryptography and reaching its true decentralization potential. One of my aims is to change all that. Bitcoin has the problem of an increasingly large carbon footprint, potential threats to it being breakable, and specialized brute force attacks that are becoming increasingly complex.
Currently, Bitcoin is quite limited in regards to its cryptography and reaching its true decentralization potential. One of my aims is to change all that. Bitcoin has the problem of an increasingly large carbon footprint, potential threats to it being breakable, and specialized brute force attacks that are becoming increasingly complex.
 David Mahdi gives advice on how identity-first security helps prevent no-click malware attacks from succeeding.
David Mahdi gives advice on how identity-first security helps prevent no-click malware attacks from succeeding.
 Cryptocurrencies need cryptography for two main reasons: Secure transactions and to verify these transfers.
Cryptocurrencies need cryptography for two main reasons: Secure transactions and to verify these transfers.
 What algorithm(s) to use, what is safe enough, what is not safe, which implementation, padding, what type of key, encoding, etc
What algorithm(s) to use, what is safe enough, what is not safe, which implementation, padding, what type of key, encoding, etc
 When envisioning pop culture, depending on what generation you might be born into, the perceptions range from HAL 9000’s glowing Red Eye from 2001 to Ava from Ex-Machina. However, the most modern concept of pop culture comes hand in hand with artificial intelligence. To make the experience wholesome, we look at artificial intelligence or specifically, machine language and cryptography as sister fields to see the implications of the phenomena in modern-day culture as well as in the times to come.
When envisioning pop culture, depending on what generation you might be born into, the perceptions range from HAL 9000’s glowing Red Eye from 2001 to Ava from Ex-Machina. However, the most modern concept of pop culture comes hand in hand with artificial intelligence. To make the experience wholesome, we look at artificial intelligence or specifically, machine language and cryptography as sister fields to see the implications of the phenomena in modern-day culture as well as in the times to come.
 What is ERC-4337? The ERC-4337 standard allows account abstraction and wallet recovery. Understanding the EIP-4337 proposal and how it secures your crypto.
What is ERC-4337? The ERC-4337 standard allows account abstraction and wallet recovery. Understanding the EIP-4337 proposal and how it secures your crypto.
 Cryptography is the core of cryptocurrency, and without it, none of the transactions will be secured, nor the integrity of any information is upheld.
Cryptography is the core of cryptocurrency, and without it, none of the transactions will be secured, nor the integrity of any information is upheld.
 Cybercriminals have turned to utilizing a variety of tools and strategies aimed to target cryptocurrency exchange customers, steal their money, or steal.
Cybercriminals have turned to utilizing a variety of tools and strategies aimed to target cryptocurrency exchange customers, steal their money, or steal.
 A gas efficient alternative to ECDSA and Merkle Trees for airdrops and presales.
A gas efficient alternative to ECDSA and Merkle Trees for airdrops and presales.
 How Edgar Allan Poe introduced early cryptography to the masses as a master cipher solver — engaging tech, literary, and crypto communities to this day.
How Edgar Allan Poe introduced early cryptography to the masses as a master cipher solver — engaging tech, literary, and crypto communities to this day.
 Introduction to Federated Learning for Data Scientists on how to access sensitive datasets for training and evaluating Machine Learning Models
Introduction to Federated Learning for Data Scientists on how to access sensitive datasets for training and evaluating Machine Learning Models
 The particular challenge I'm speaking of is cleverly called Krypton, because it’s a crypto challenge, on the main page you are given hints and examples.
The particular challenge I'm speaking of is cleverly called Krypton, because it’s a crypto challenge, on the main page you are given hints and examples.
 The purpose of cryptography is to keep information private, and the purpose of open-source is to make code public... So we shouldn't we open source our cryptography algorithms right?
The purpose of cryptography is to keep information private, and the purpose of open-source is to make code public... So we shouldn't we open source our cryptography algorithms right?
 Need to encrypt some text with a password or private key in Python? You certainly came to the right place. AES-256 is a solid symmetric cipher that is commonly used to encrypt data for oneself. In other words, the same person who is encrypting the data is typically decrypting it as well (think password manager).
Need to encrypt some text with a password or private key in Python? You certainly came to the right place. AES-256 is a solid symmetric cipher that is commonly used to encrypt data for oneself. In other words, the same person who is encrypting the data is typically decrypting it as well (think password manager).
 Protocols are not handed down from on high. On the contrary, they start as a seed, which grows into a massive tree (if it’s worthy, and more importantly, if it’s nurtured). These seeds are no more than ideas, planted by individuals, perhaps in a Slack channel or, more formally, as an RFC.
Protocols are not handed down from on high. On the contrary, they start as a seed, which grows into a massive tree (if it’s worthy, and more importantly, if it’s nurtured). These seeds are no more than ideas, planted by individuals, perhaps in a Slack channel or, more formally, as an RFC.
 By the time of writing of this article everyone knows, the "technologies of the future" as listed from various mainstream media. And I agree with most of them. It is worth discussing a few not so obvious though. I expect my "predictions" to be fulfilled by 2030.
By the time of writing of this article everyone knows, the "technologies of the future" as listed from various mainstream media. And I agree with most of them. It is worth discussing a few not so obvious though. I expect my "predictions" to be fulfilled by 2030.
 Building a from-scratch server or using a lightweight framework is empowering. With that power comes responsibility, specifically the responsibility to securely store user’s passwords.
Building a from-scratch server or using a lightweight framework is empowering. With that power comes responsibility, specifically the responsibility to securely store user’s passwords.
 We have long sought secure ways to exchange data. Some current methods include cryptography, hashing and requiring the solution of math problems that demand enormous computing power. Quantum computing could render some of our current methods insecure and obsolete, while enabling new methods.
We have long sought secure ways to exchange data. Some current methods include cryptography, hashing and requiring the solution of math problems that demand enormous computing power. Quantum computing could render some of our current methods insecure and obsolete, while enabling new methods.
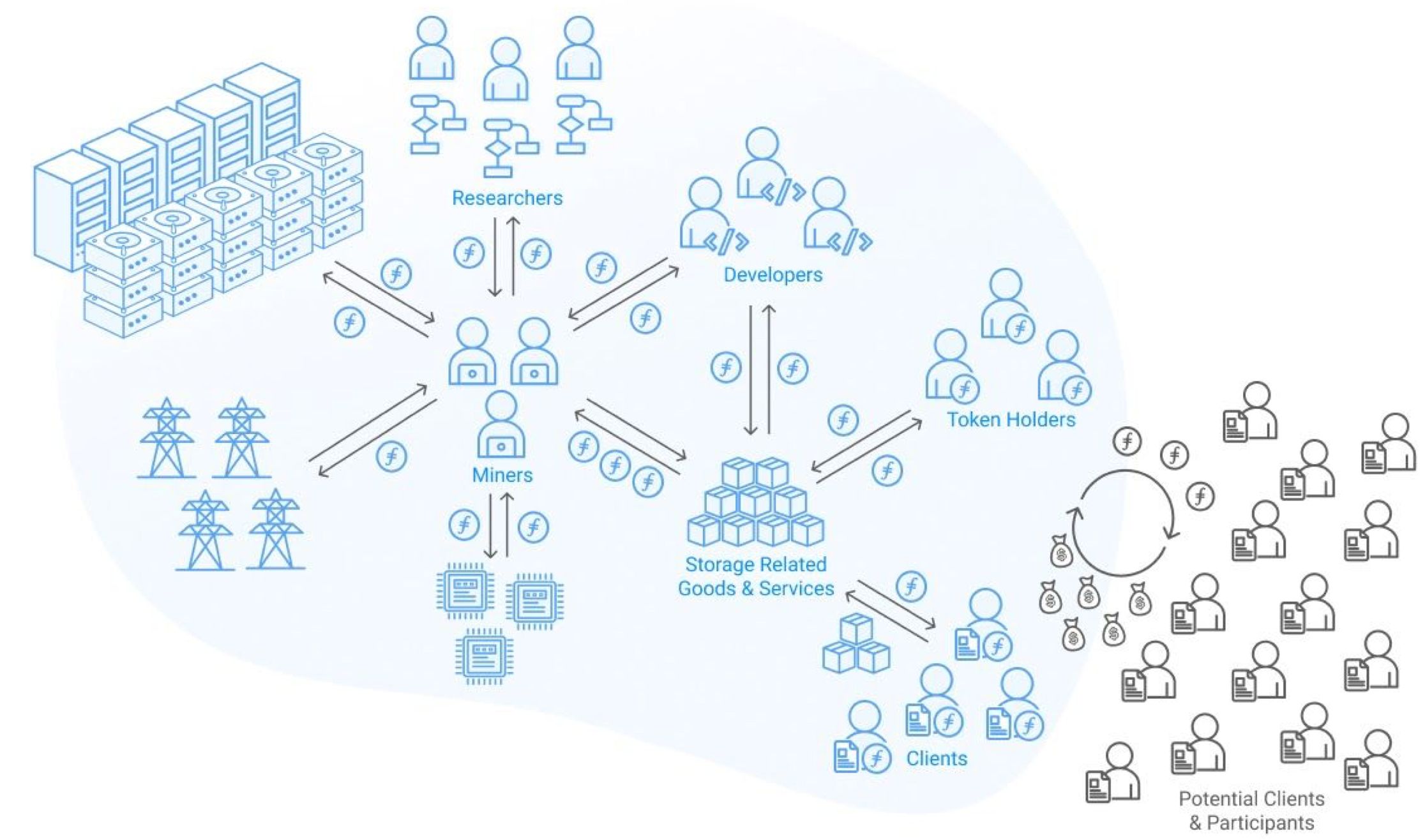
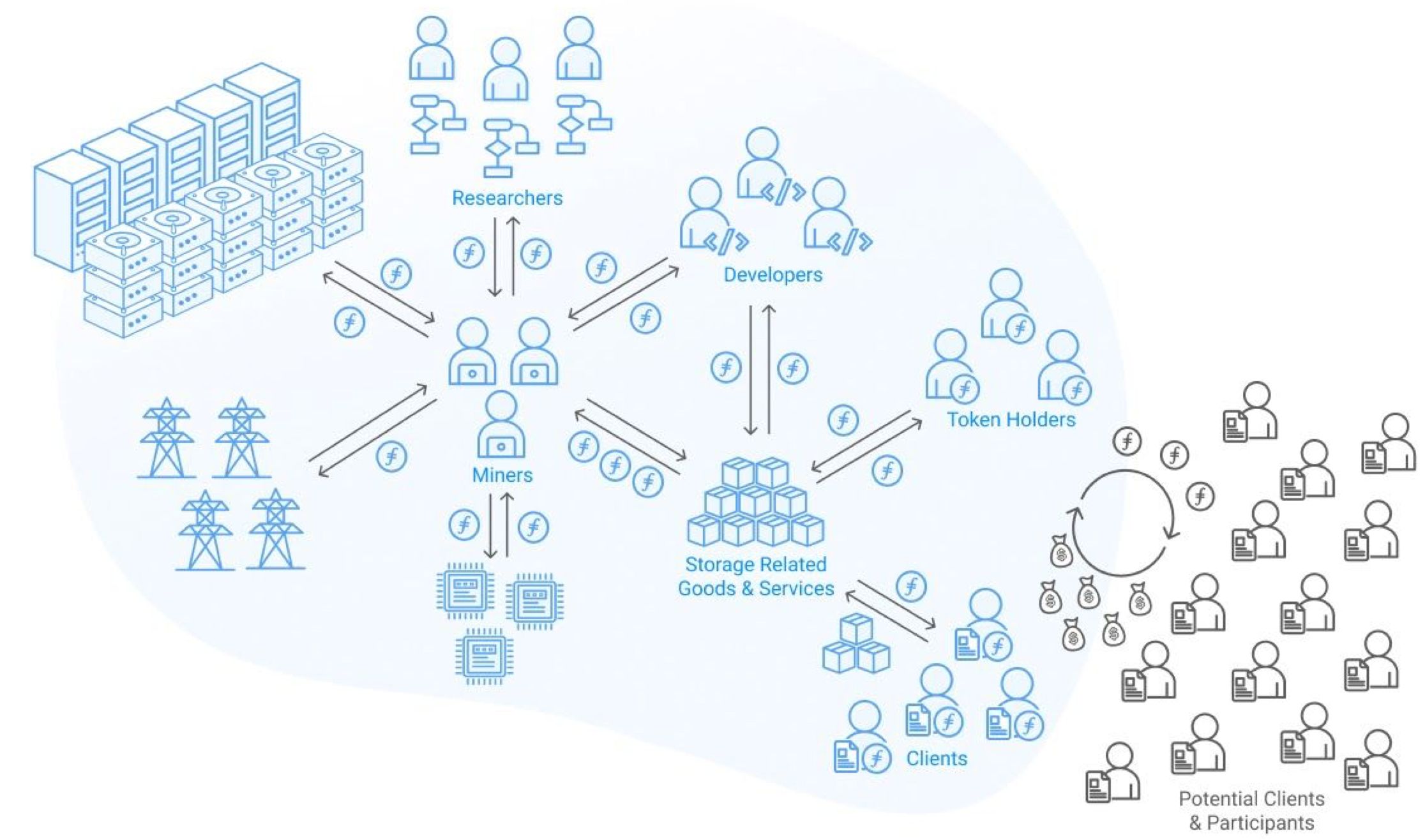 On Web2 or the traditional web, storage systems were designed to suit
fast-growing, collaborative environments. These storage systems boasted different degrees of data availability and data security and protection from loss. As Web2 grew in adoption so did the generation of Web2 data volume and density in many formats. This data could be large files, non-transactional, often created by a single user, and may be shared over some geographical distance. This design led to the reliance on central authorities to store the world's data.
On Web2 or the traditional web, storage systems were designed to suit
fast-growing, collaborative environments. These storage systems boasted different degrees of data availability and data security and protection from loss. As Web2 grew in adoption so did the generation of Web2 data volume and density in many formats. This data could be large files, non-transactional, often created by a single user, and may be shared over some geographical distance. This design led to the reliance on central authorities to store the world's data.
 ZKP can be used for much more than just privacy. ZKPs are so versatile that it may redefine how blockchains work.
ZKP can be used for much more than just privacy. ZKPs are so versatile that it may redefine how blockchains work.
 Hi, Joey Trend here! Lately the bitcoin, bcash, and bsv communities have been at war. We should stop the fight against one another. Instead, we should start the fight against fiat currency.
Hi, Joey Trend here! Lately the bitcoin, bcash, and bsv communities have been at war. We should stop the fight against one another. Instead, we should start the fight against fiat currency.
 Password generators are now in abundance. Particularly surprising are the many web applications for this purpose.
Password generators are now in abundance. Particularly surprising are the many web applications for this purpose.
 Go is becoming very popular for backend web development, and JWT's are one of the most popular ways to handle authentication on API requests. In this article, we are going to go over the basics of JWT's and how to implement a secure authentication strategy in Go!
Go is becoming very popular for backend web development, and JWT's are one of the most popular ways to handle authentication on API requests. In this article, we are going to go over the basics of JWT's and how to implement a secure authentication strategy in Go!
 The Finney testnet was launched to avoid future Sybil attacks.
The Finney testnet was launched to avoid future Sybil attacks.
 Stevie is a FinTech editor and co-founder of Womxn In Crypto, an educational community obsessed with Bitcoin and blockchain tech. She loves cryptography!
Stevie is a FinTech editor and co-founder of Womxn In Crypto, an educational community obsessed with Bitcoin and blockchain tech. She loves cryptography!
 Permutations over Lagrange-bases for Oecumenical Noninteractive arguments of Knowledge, or PLONKS are a new general-purpose zer-knowledge proof scheme.
Permutations over Lagrange-bases for Oecumenical Noninteractive arguments of Knowledge, or PLONKS are a new general-purpose zer-knowledge proof scheme.
 Have a good look at the apps you have on your Android phone. How do you ensure all of them are authentic? E.g. how can you make sure that the Instagram app that you have on your mobile is a genuine one and not a copy or fake app.
Have a good look at the apps you have on your Android phone. How do you ensure all of them are authentic? E.g. how can you make sure that the Instagram app that you have on your mobile is a genuine one and not a copy or fake app.
 Politicians in the United States have been claiming recently that end-to-end encryption is certainly too dangerous to permit. This movement is serious. Congress even introduced a bill that would remove the protections that we currently have that allow us to legally encrypt information. Lindsey Graham is one such proponent of this restrictive legislation:
Politicians in the United States have been claiming recently that end-to-end encryption is certainly too dangerous to permit. This movement is serious. Congress even introduced a bill that would remove the protections that we currently have that allow us to legally encrypt information. Lindsey Graham is one such proponent of this restrictive legislation:
 Many people think that Bitcoin, Ethereum, and other public blockchains all offer privacy by default. Unfortunately, that is not the case
Many people think that Bitcoin, Ethereum, and other public blockchains all offer privacy by default. Unfortunately, that is not the case
 With the third episode of our shared journey, we will uncover the meaning of the hashing function, share a ride on the Avalanche effect, and much more!
With the third episode of our shared journey, we will uncover the meaning of the hashing function, share a ride on the Avalanche effect, and much more!
 This article talks about zero-knowledge proof and how zero-knowledge proofs work establishing trust with technology.
This article talks about zero-knowledge proof and how zero-knowledge proofs work establishing trust with technology.
 If you’ve never had this experience you have my envy. You’re on a development team and one of the developers does sloppy work and there is nothing you can do about it.
If you’ve never had this experience you have my envy. You’re on a development team and one of the developers does sloppy work and there is nothing you can do about it.
 In case you are not in raptures when corporations persistently feed you with targeted advertising and 'bad guys' gain access to your private data, probably you need to replace your email service to more secure analogue with reliable encryption.
In case you are not in raptures when corporations persistently feed you with targeted advertising and 'bad guys' gain access to your private data, probably you need to replace your email service to more secure analogue with reliable encryption.
 This post is about one of the topics we get asked about the most: guaranteeing webhook ordering.
This post is about one of the topics we get asked about the most: guaranteeing webhook ordering.
 history, concepts, principles, technical implementation, and development status of zero-knowledge proofs in the simplest language ever
history, concepts, principles, technical implementation, and development status of zero-knowledge proofs in the simplest language ever
 Being concerned with the security of online communication and information exchange is absolutely OK. It is a reflection of the fact that you
are aware of global surveillance happening every second of our presence online. Our online activities are monitored, intercepted, collected, and stored. And now imagine that what you know is only the small fraction of what is really happening with our information.
Being concerned with the security of online communication and information exchange is absolutely OK. It is a reflection of the fact that you
are aware of global surveillance happening every second of our presence online. Our online activities are monitored, intercepted, collected, and stored. And now imagine that what you know is only the small fraction of what is really happening with our information.
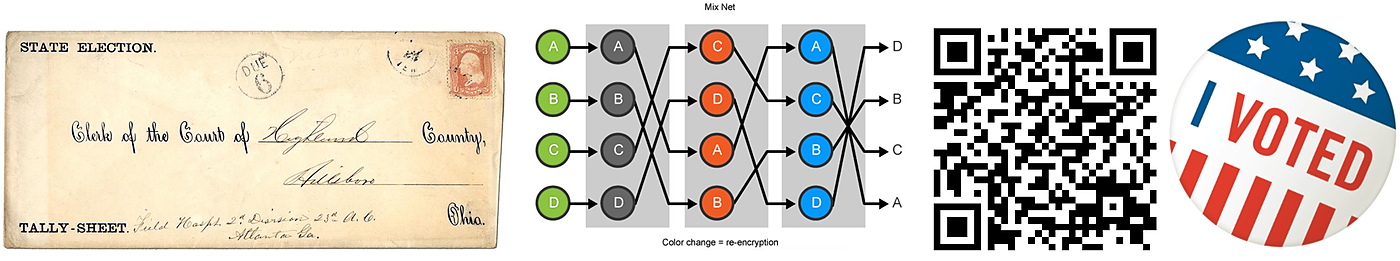
 The Senate Intelligence Committee recently released a report detailing Russia’s interference in the 2016 election. Russian interference is nothing new – discourse since 2016 has focused on Russia’s (technically legal) social engineering and manipulation of social networks. The report, however, confirms Russia’s definitively illegal interference with electronic voting systems, and “the US was unprepared at all levels of government for a concerted attack from a determined foreign adversary on our election infrastructure,” said Committee Chairman Richard Burr in an accompanying statement.
The Senate Intelligence Committee recently released a report detailing Russia’s interference in the 2016 election. Russian interference is nothing new – discourse since 2016 has focused on Russia’s (technically legal) social engineering and manipulation of social networks. The report, however, confirms Russia’s definitively illegal interference with electronic voting systems, and “the US was unprepared at all levels of government for a concerted attack from a determined foreign adversary on our election infrastructure,” said Committee Chairman Richard Burr in an accompanying statement.
Given American technological capabilities, how was this interference possible?
Voting is still in the dark ages
Voting lies at the heart of democracy, yet it has failed to make the same technological advancements that we’ve come to expect in other facets of our lives. Almost five decades into the “digital revolution,” we still consider paper ballots the “secure” standard for choosing leadership.
Why don’t we vote electronically?
Implicit in our trust of paper-based systems is a distrust of technology. Although technology has the potential to revolutionize the democratic process, the digital voting systems currently in place are often far from secure.
Today’s electronic ballot boxes, when implemented incorrectly, pose astonishing risks: For example, the US’ electronic ballot systems (called DRE, which stands for “direct electronic recording”) have notoriously relied on Windows XP, a software released in 2001. In 2014, security expert Carsten Schuermann hacked into a DRE machine over a Wi-Fi network in mere minutes by exploiting Windows XP’s old security protocols.
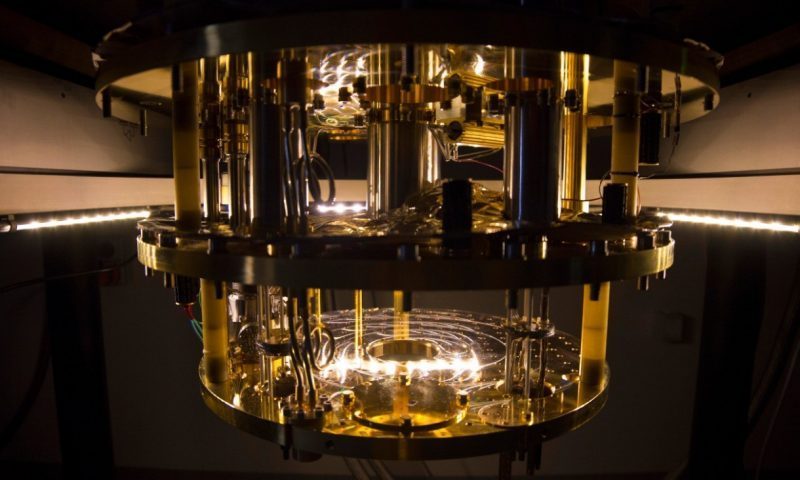 With quantum computers getting more powerful every year, many worry about the safety of modern encryption standards. As quantum computers improve in performance and the number of qubits used for calculations increase, current crypto systems are under more threat of attack.
With quantum computers getting more powerful every year, many worry about the safety of modern encryption standards. As quantum computers improve in performance and the number of qubits used for calculations increase, current crypto systems are under more threat of attack.
 Satoshi Nakamoto — the maverick inventor of Bitcoin — not only saw a pregnant future but also made us its midwives as well.
Satoshi Nakamoto — the maverick inventor of Bitcoin — not only saw a pregnant future but also made us its midwives as well.
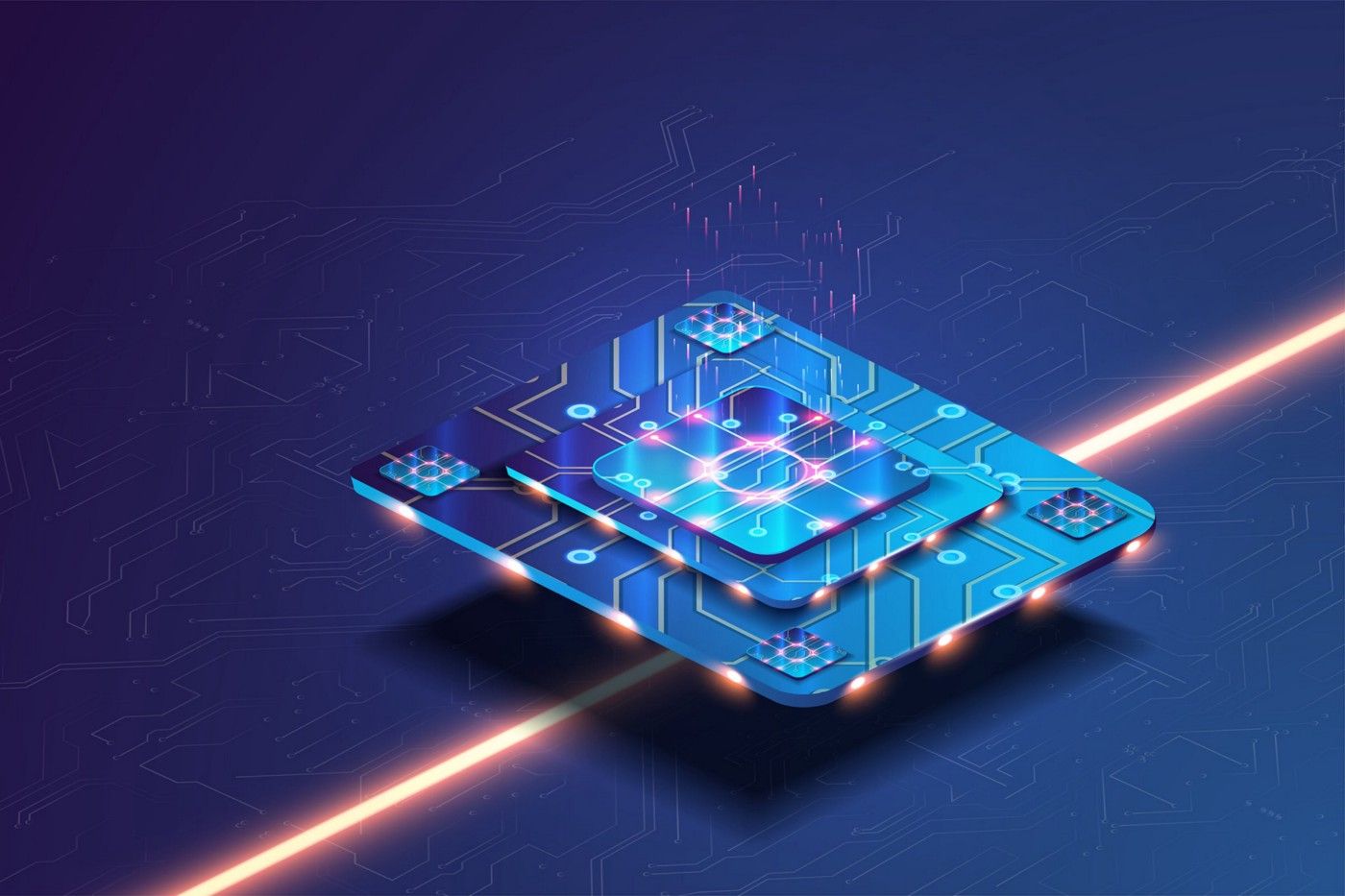
 Next Generation Semiconductors: Designing accelerators for advanced cryptography
Next Generation Semiconductors: Designing accelerators for advanced cryptography
 Brute force attackers guess passwords, passphrases, and private keys in an attempt to eventually get the right answer and crack the security of a system, but how do they know when they have the right key?
Brute force attackers guess passwords, passphrases, and private keys in an attempt to eventually get the right answer and crack the security of a system, but how do they know when they have the right key?
 Recently I’ve been refactoring the tests for a gem I maintain and I needed to test that it sets the right cookies at the right time. But the cookies in use in the gem are signed cookies and that caused a slight hiccup for me. I’d never tested the value in a signed cookie before and it wasn’t immediately obvious what to do.
Recently I’ve been refactoring the tests for a gem I maintain and I needed to test that it sets the right cookies at the right time. But the cookies in use in the gem are signed cookies and that caused a slight hiccup for me. I’d never tested the value in a signed cookie before and it wasn’t immediately obvious what to do.
 Anyone who has seen the movie The Imitation Game, or studied computer science in school, probably has at least a brief understanding of Enigma, Alan Turing, and some of the other fun cryptography that went on during WWII. During this time and until the 1970's, governments from around the world had near total control of all cryptographic systems.
Anyone who has seen the movie The Imitation Game, or studied computer science in school, probably has at least a brief understanding of Enigma, Alan Turing, and some of the other fun cryptography that went on during WWII. During this time and until the 1970's, governments from around the world had near total control of all cryptographic systems.
 At present it is almost impossible to live our day-to-day lives without transacting online or using the internet for our social interactions. As of 2019 there are over 4 billion active internet users – more than half the world’s population – and worldwide the average person spends 6 hours and 42 minutes online each day.
At present it is almost impossible to live our day-to-day lives without transacting online or using the internet for our social interactions. As of 2019 there are over 4 billion active internet users – more than half the world’s population – and worldwide the average person spends 6 hours and 42 minutes online each day.
 I want to talk a little about how you can use content-based addressing (aka data fingerprinting) as a general approach to make your applications faster and more secure with some practical JavaScript examples.
I want to talk a little about how you can use content-based addressing (aka data fingerprinting) as a general approach to make your applications faster and more secure with some practical JavaScript examples.
 For the time being, I want you p33ps to ignore the general meaning of these words used in daily context and give a new meaning to them for the current time being.
For the time being, I want you p33ps to ignore the general meaning of these words used in daily context and give a new meaning to them for the current time being.
 I’ve decided to write an ELI15 for zk-SNARK jargon since I’ve yet to come across something similar during my studies.
I’ve decided to write an ELI15 for zk-SNARK jargon since I’ve yet to come across something similar during my studies.
 In cryptography, encryption is the conversion of cleartext into a coded text or ciphertext. A ciphertext is intended to be unreadable by unauthorized readers.
In cryptography, encryption is the conversion of cleartext into a coded text or ciphertext. A ciphertext is intended to be unreadable by unauthorized readers.
 As video content evolves, so should the security of your videos. Learn how to safeguard your videos using an NFT marketplace and advanced cryptography.
As video content evolves, so should the security of your videos. Learn how to safeguard your videos using an NFT marketplace and advanced cryptography.
 Welcome to the SNARK Age, a pop-up newsletter exploring and celebrating a technology that we believe will have fundamental and deterministic impacts on privacy, computing, cryptography, and money in the years to come. We’ll be sharing (mostly) bite-sized issues highlighting the key events, milestones and people in the space.
Welcome to the SNARK Age, a pop-up newsletter exploring and celebrating a technology that we believe will have fundamental and deterministic impacts on privacy, computing, cryptography, and money in the years to come. We’ll be sharing (mostly) bite-sized issues highlighting the key events, milestones and people in the space.
 Software Engineering != Computer Science
Software Engineering != Computer Science
 There are many different methods to verify a user’s identification. Although the management of authentication and active sessions has come a long way, simple password authentication has not been able to provide sufficient security to support the rapid growth in data, advancements in mobile and cloud technologies, and increasing volumes of security breaches.
There are many different methods to verify a user’s identification. Although the management of authentication and active sessions has come a long way, simple password authentication has not been able to provide sufficient security to support the rapid growth in data, advancements in mobile and cloud technologies, and increasing volumes of security breaches.
 Adi Shamir’s secret sharing is an algorithm used to share ownership of a secret among a group of participants. In order to calculate the original secret, a minimum number of shares must be used.
Adi Shamir’s secret sharing is an algorithm used to share ownership of a secret among a group of participants. In order to calculate the original secret, a minimum number of shares must be used.
 Don’t get me wrong, it’s a funny title. It starts with how, whereas when you read it you probably wondered why.
Don’t get me wrong, it’s a funny title. It starts with how, whereas when you read it you probably wondered why.
 White-box cryptography combines methods of encryption and obfuscation to embed secret keys within application code. The goal is to combine code and keys in such a way that the two are indistinguishable to an attacker, and the new "white-box" program can be safely run in an insecure environment.
White-box cryptography combines methods of encryption and obfuscation to embed secret keys within application code. The goal is to combine code and keys in such a way that the two are indistinguishable to an attacker, and the new "white-box" program can be safely run in an insecure environment.
 Since the launch of Bitcoin in 2008, four trader archetypes have arrived to scoop up crypto gains and minimize crypto losses.
Since the launch of Bitcoin in 2008, four trader archetypes have arrived to scoop up crypto gains and minimize crypto losses.
 Cryptographic Hash Functions are a class of hash functions that are cryptographically secure. From password authentication and integrity verification to blockchain—these functions are used in a multitude of applications.
Cryptographic Hash Functions are a class of hash functions that are cryptographically secure. From password authentication and integrity verification to blockchain—these functions are used in a multitude of applications.
 Make use of your downtime and read something good!
Make use of your downtime and read something good!
 Constants can be confusing and easy to misuse in Go if you are coming from an untyped language. In this article we will learn what constants are, and when it is best to make use of them.
Constants can be confusing and easy to misuse in Go if you are coming from an untyped language. In this article we will learn what constants are, and when it is best to make use of them.
 Cryptography Interference With Blockchain
Cryptography Interference With Blockchain
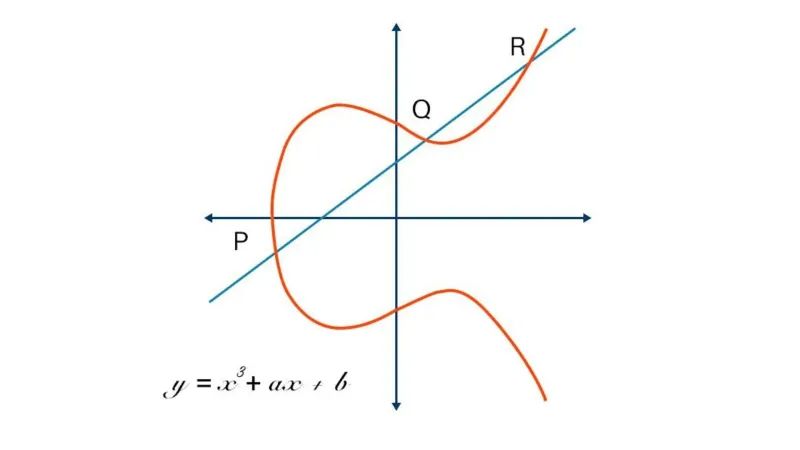
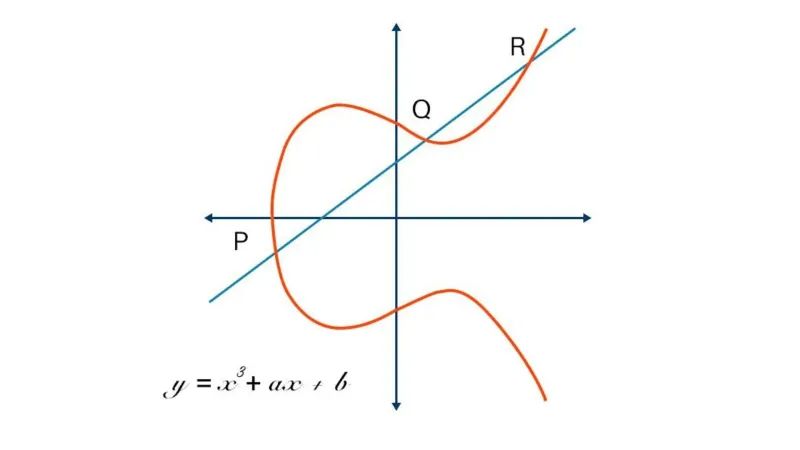 Elliptic Curve Cryptography (ECC) is a modern public-key encryption technique famous for being smaller, faster, and more efficient than incumbents.
Elliptic Curve Cryptography (ECC) is a modern public-key encryption technique famous for being smaller, faster, and more efficient than incumbents.
 Today we’re announcing cross-chain zaps integration into the Symbiosis protocol.
Today we’re announcing cross-chain zaps integration into the Symbiosis protocol.
 Reasonable security through architecture
Reasonable security through architecture
 Cryptography provides a method for secure communication. It stops unauthorized parties from gaining access to messages between authorized parties.
Cryptography provides a method for secure communication. It stops unauthorized parties from gaining access to messages between authorized parties.
 The Web Crypto API is an interface allowing a script to use cryptographic primitives in order to build systems using cryptography.
The Web Crypto API is an interface allowing a script to use cryptographic primitives in order to build systems using cryptography.
 NFTs are the digitized form of any artwork, and the people interested in these artworks can buy them from NFT marketplaces.
NFTs are the digitized form of any artwork, and the people interested in these artworks can buy them from NFT marketplaces.
 In this article, we are going to build a simple Ethereum wallet from scratch using Python. During the process, we will use some cryptography and try to interact with the Ethereum blockchain. In part 1, we will generate a key pair which is compatible with the Ethereum protocol, obtain the Ethereum address from the public key and encrypt the private key using a password.
In this article, we are going to build a simple Ethereum wallet from scratch using Python. During the process, we will use some cryptography and try to interact with the Ethereum blockchain. In part 1, we will generate a key pair which is compatible with the Ethereum protocol, obtain the Ethereum address from the public key and encrypt the private key using a password.
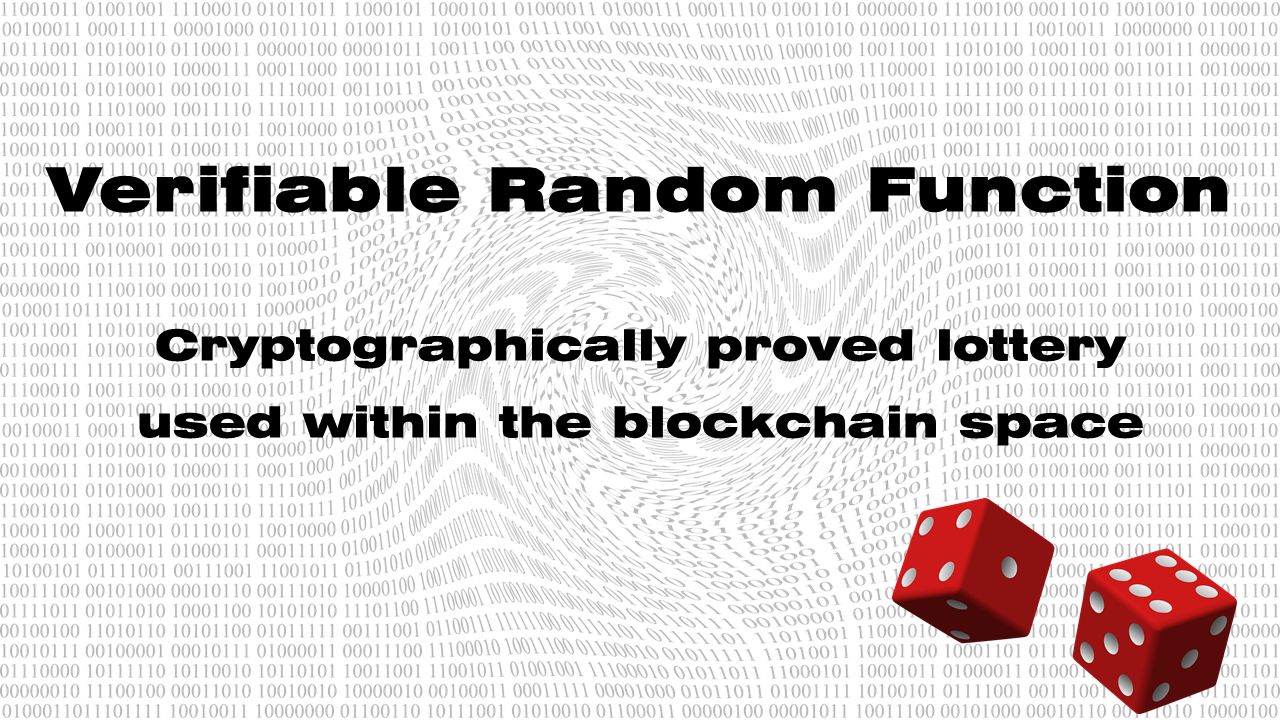
 Blockchains such as Bitcoin are facing a key problem. How to fairly spread out the decision-making consensus on what pool will win the competition and have the right to add the new block into the blockchain itself.
Blockchains such as Bitcoin are facing a key problem. How to fairly spread out the decision-making consensus on what pool will win the competition and have the right to add the new block into the blockchain itself.
 Secure context
This feature is available only in secure contexts (HTTPS), in some or all supporting browsers.
Secure context
This feature is available only in secure contexts (HTTPS), in some or all supporting browsers.
 I bet you created at least once an RSA key pair, usually because you needed to connect to GitHub and you wanted to avoid typing your password every time. You diligently followed the documentation on how to create SSH keys and after a couple of minutes your setup was complete.
I bet you created at least once an RSA key pair, usually because you needed to connect to GitHub and you wanted to avoid typing your password every time. You diligently followed the documentation on how to create SSH keys and after a couple of minutes your setup was complete.
 Quantum cryptography creates cryptosystems based on quantum mechanics rather than a complex math problem. It is a mature tech that's in rivalry with Blockchain.
Quantum cryptography creates cryptosystems based on quantum mechanics rather than a complex math problem. It is a mature tech that's in rivalry with Blockchain.
 A key derivation function, or KDF, derives one or many secret keys from a secret value. Therefore, If you've ever needed to store a password in a database or create a private key from a password, you may have used a KDF.
A key derivation function, or KDF, derives one or many secret keys from a secret value. Therefore, If you've ever needed to store a password in a database or create a private key from a password, you may have used a KDF.
 Most of us are probably wondering why the world today’s going to development of new generation of computer called Quantum-Computer
Most of us are probably wondering why the world today’s going to development of new generation of computer called Quantum-Computer
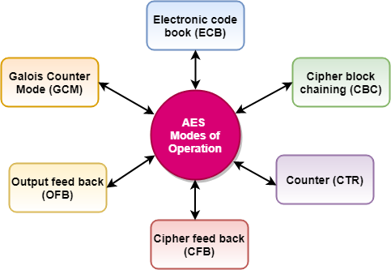
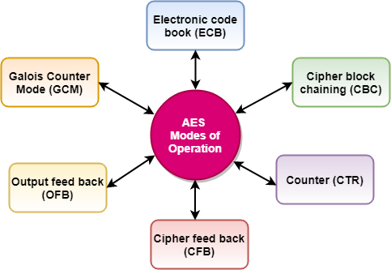 The AES encryption algorithm is a block cipher consist of a block length of 128 bits that uses the same encryption key to perform several rounds of encryption.
The AES encryption algorithm is a block cipher consist of a block length of 128 bits that uses the same encryption key to perform several rounds of encryption.
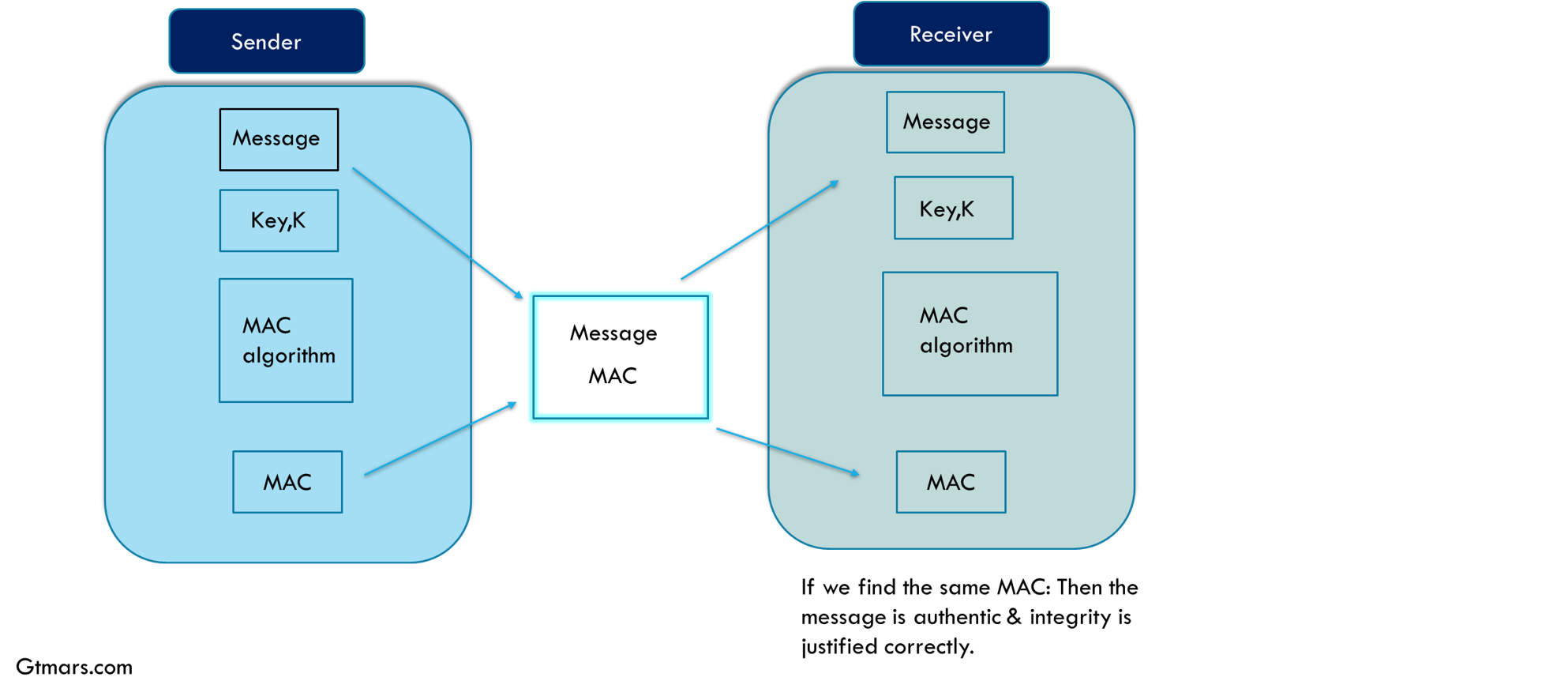
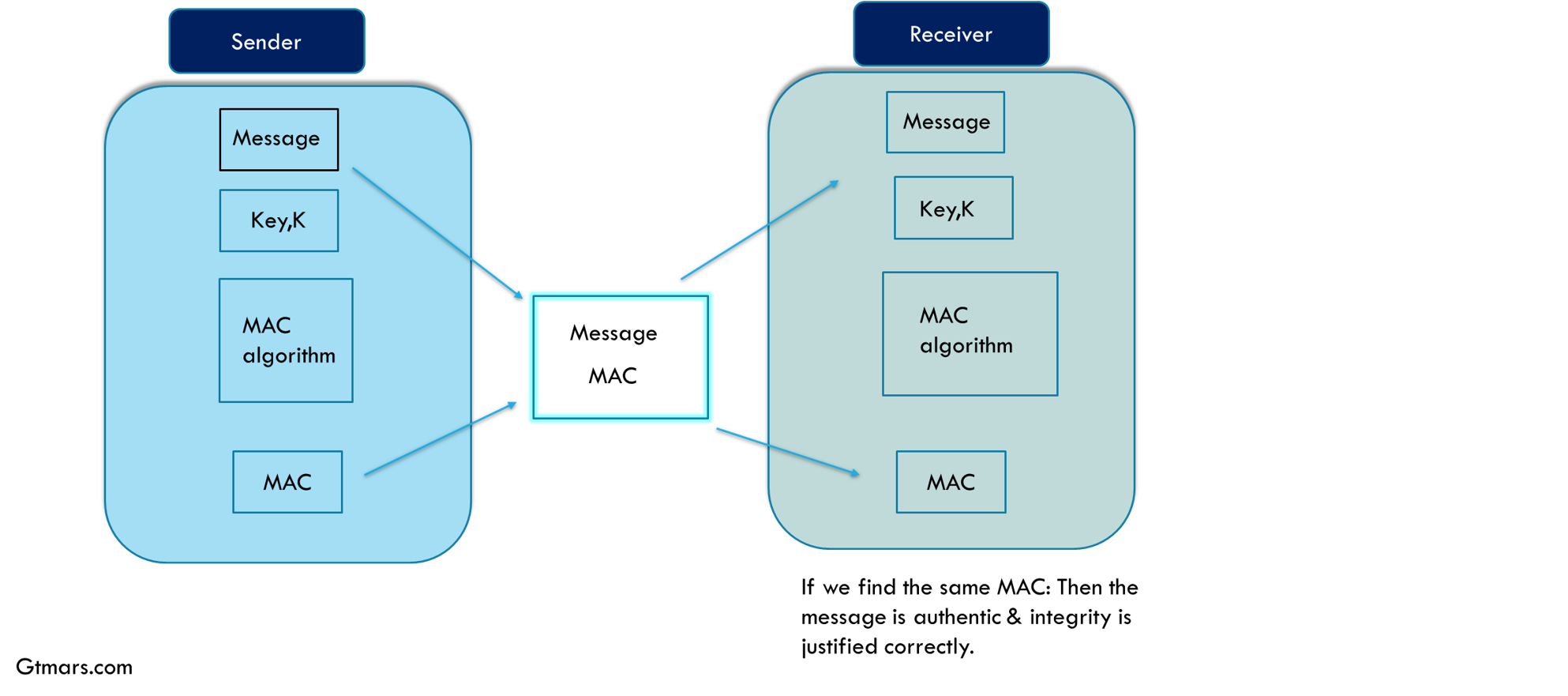
 HMACs and MACs are authentication codes and are often the backbone of JWT authentication systems. Let's take a look at how they work!
HMACs and MACs are authentication codes and are often the backbone of JWT authentication systems. Let's take a look at how they work!
 What is Cryptography?
What is Cryptography?

 From Caesar's cipher to RSA. A deep dive into the inner workings of modern cryptography and its potential crumbling.
From Caesar's cipher to RSA. A deep dive into the inner workings of modern cryptography and its potential crumbling.
 ZPrize Competition. Over $2 million of cash prizes! The goal of ZPrize is to bring together the best teams at the intersection of cryptography research.
ZPrize Competition. Over $2 million of cash prizes! The goal of ZPrize is to bring together the best teams at the intersection of cryptography research.
 Are we at the cradle of a quantum age?
Are we at the cradle of a quantum age?
 There is a lot of enthusiasm for the application of zero-knowledge proof systems, at Dusk Network we’ve developed the open-source PLONK zero-knowledge proof system. It can be used for many things, and what better way to demonstrate its potential with an example!
There is a lot of enthusiasm for the application of zero-knowledge proof systems, at Dusk Network we’ve developed the open-source PLONK zero-knowledge proof system. It can be used for many things, and what better way to demonstrate its potential with an example!
 Today Zoom acquired Keybase. It came as a shock to me at first; but, it shouldn't surprise us.
Today Zoom acquired Keybase. It came as a shock to me at first; but, it shouldn't surprise us.
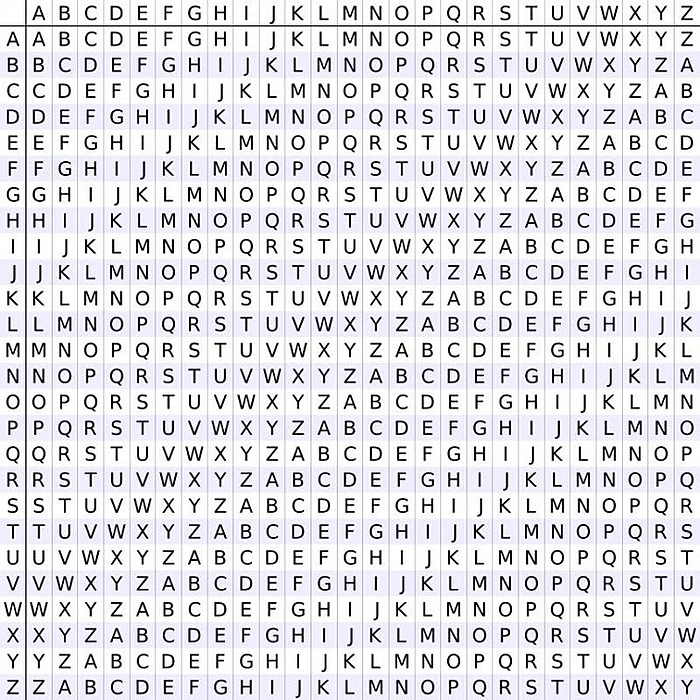
 Hi again and welcome back to part 2 of the basic cryptography. Previously we discuss about what is cryptography and how fundamental and ancient problem it is in communication science. We talk about ceaser's cipher and how easy it is to break. We also talk about Substitution Cipher which was slight improvement to Ceaser' cipher but can easily be cracked using Frequency analysis technique.
Hi again and welcome back to part 2 of the basic cryptography. Previously we discuss about what is cryptography and how fundamental and ancient problem it is in communication science. We talk about ceaser's cipher and how easy it is to break. We also talk about Substitution Cipher which was slight improvement to Ceaser' cipher but can easily be cracked using Frequency analysis technique.
 Wars can be fought in the real world but there is also a virtual battlefield - and it is just as harmful. The Lawful Access to Encrypted Data Act is the latest attempt to access people's encrypted data and it serves as another reinforcement.
Wars can be fought in the real world but there is also a virtual battlefield - and it is just as harmful. The Lawful Access to Encrypted Data Act is the latest attempt to access people's encrypted data and it serves as another reinforcement.
 As the world finds itself preoccupied with COVID-19, the United States government is trying to pass a law to ban encryption. It's called the EARN IT act, and while it claims to combat the sexual exploitation of children online, it has potentially devastating repercussions for encryption and companies that use it to protect your privacy online.
As the world finds itself preoccupied with COVID-19, the United States government is trying to pass a law to ban encryption. It's called the EARN IT act, and while it claims to combat the sexual exploitation of children online, it has potentially devastating repercussions for encryption and companies that use it to protect your privacy online.
 Cypherpunks hold an ideology that states that privacy is an essential component of freedom and without privacy, one cannot have true freedom of speech.
Cypherpunks hold an ideology that states that privacy is an essential component of freedom and without privacy, one cannot have true freedom of speech.
 This is a topic that has been talked about quite a bit, but I think it's an important one to reiterate to our users.
This is a topic that has been talked about quite a bit, but I think it's an important one to reiterate to our users.
 Over the last decade, there’s been a massive outburst of internet users across the globe. Simultaneously, there’s been a growing penetration of different digital and paperless technologies across businesses and organizations.
Over the last decade, there’s been a massive outburst of internet users across the globe. Simultaneously, there’s been a growing penetration of different digital and paperless technologies across businesses and organizations.
 The most common mistake is that blockchain — the database. This error is often even allowed to be used by crypto leaders.
The most common mistake is that blockchain — the database. This error is often even allowed to be used by crypto leaders.
 Once upon a time, a company I worked for had a problem: We had thousands of messages flowing through our data pipeline each second, and we want to be able to send email and SMS alerts to ours users when messages matching specific criteria were seen.
Once upon a time, a company I worked for had a problem: We had thousands of messages flowing through our data pipeline each second, and we want to be able to send email and SMS alerts to ours users when messages matching specific criteria were seen.
 Exploring fully homomorphic encryption which, for a long time been considered one of the holy grails of cryptography.
Exploring fully homomorphic encryption which, for a long time been considered one of the holy grails of cryptography.
 One of the most powerful types of cryptography being used nowadays is Elliptic Curve Cryptography. This method is used to secure, among others, the Cloudflare
One of the most powerful types of cryptography being used nowadays is Elliptic Curve Cryptography. This method is used to secure, among others, the Cloudflare
 Over four and half billion people, or fifty-nine per cent of the global population, use the Internet every day. The Internet is where we communicate, transact, and consume information.
Over four and half billion people, or fifty-nine per cent of the global population, use the Internet every day. The Internet is where we communicate, transact, and consume information.
 A smart city is representative of urbanization in the digital world. The infrastructure of smart cities is built on embedded Internet of Things (IoT) technology. The smart city promises new opportunities and growth in the urban world. These opportunities include better connectivity, productivity, agility, and innovation. However, it is a known fact that with opportunities come challenges.
A smart city is representative of urbanization in the digital world. The infrastructure of smart cities is built on embedded Internet of Things (IoT) technology. The smart city promises new opportunities and growth in the urban world. These opportunities include better connectivity, productivity, agility, and innovation. However, it is a known fact that with opportunities come challenges.

 here are various such cryptographic primitives that are employed in blockchain, let's start with hash functions
here are various such cryptographic primitives that are employed in blockchain, let's start with hash functions
 Data integrity refers to the accuracy, legitimacy, and consistency of information in a system. When a message is sent, particularly using an untrusted medium, data integrity provides us confidence that the message wasn't tampered with.
Data integrity refers to the accuracy, legitimacy, and consistency of information in a system. When a message is sent, particularly using an untrusted medium, data integrity provides us confidence that the message wasn't tampered with.
 Millicent is a government-backed first-mover stablecoin. Founder Stella Dyer founded the company after growing up in the UK as a refugee from the Biafran War.
Millicent is a government-backed first-mover stablecoin. Founder Stella Dyer founded the company after growing up in the UK as a refugee from the Biafran War.
 This paper will discuss what quantum computation is and the effects it can have on the way our society works.
This paper will discuss what quantum computation is and the effects it can have on the way our society works.
 This is going to be a basic introduction to hash functions. I will assume most of my audience is here to gain an understanding of why hash functions are used and the basic idea of why they work. My goal is to explain it in a general sense, I will be omitting proofs and implementation details and instead focusing on the high-level principles.
This is going to be a basic introduction to hash functions. I will assume most of my audience is here to gain an understanding of why hash functions are used and the basic idea of why they work. My goal is to explain it in a general sense, I will be omitting proofs and implementation details and instead focusing on the high-level principles.
 There is a lot of enthusiasm for the application of zero-knowledge proof systems, at Dusk Network we’ve developed the open-source PLONK zero-knowledge proof system. It can be used for many things, and what better way to demonstrate its potential with an example!
There is a lot of enthusiasm for the application of zero-knowledge proof systems, at Dusk Network we’ve developed the open-source PLONK zero-knowledge proof system. It can be used for many things, and what better way to demonstrate its potential with an example!
 Get a better understanding of how webhooks work, when to use them and most importantly the security measures to take to use them in practice!
Get a better understanding of how webhooks work, when to use them and most importantly the security measures to take to use them in practice!
 Secure Multi-Party Computation (SMPC), as described by Wikipedia, is a subset of cryptography to create methods for multiple users to jointly compute a function over their inputs while keeping those inputs private. A significant benefit of Secure Multi-Party Computation is that it preserves data privacy while making it usable and open for analysis.
Secure Multi-Party Computation (SMPC), as described by Wikipedia, is a subset of cryptography to create methods for multiple users to jointly compute a function over their inputs while keeping those inputs private. A significant benefit of Secure Multi-Party Computation is that it preserves data privacy while making it usable and open for analysis.
 An introduction to this privacy-preserving cryptographic technique and how Keyless is using it to transform the way we share and store private data across the internet.
An introduction to this privacy-preserving cryptographic technique and how Keyless is using it to transform the way we share and store private data across the internet.
 A short story about how national secrets, passwords, and financial data stays secret because of a small handful of smart people playing "Bet you can't"
A short story about how national secrets, passwords, and financial data stays secret because of a small handful of smart people playing "Bet you can't"
 “That’s so random!” Common phrase used to express something is unexpected or without a pattern. Does random mean something different in science?
“That’s so random!” Common phrase used to express something is unexpected or without a pattern. Does random mean something different in science?
 Whether through social engineering, phishing scams, or ransomware attacks ultimately it is just a hacker and his classic computer, all that pretty much expected
Whether through social engineering, phishing scams, or ransomware attacks ultimately it is just a hacker and his classic computer, all that pretty much expected
 Post-quantum cryptography will involve a significant transition, and if we are not cautious, we risk experiencing the same security problems again.
Post-quantum cryptography will involve a significant transition, and if we are not cautious, we risk experiencing the same security problems again.
 A social graph is a mapping of social relationships between individuals. It reflects the people and their interactions through various channels.
A social graph is a mapping of social relationships between individuals. It reflects the people and their interactions through various channels.
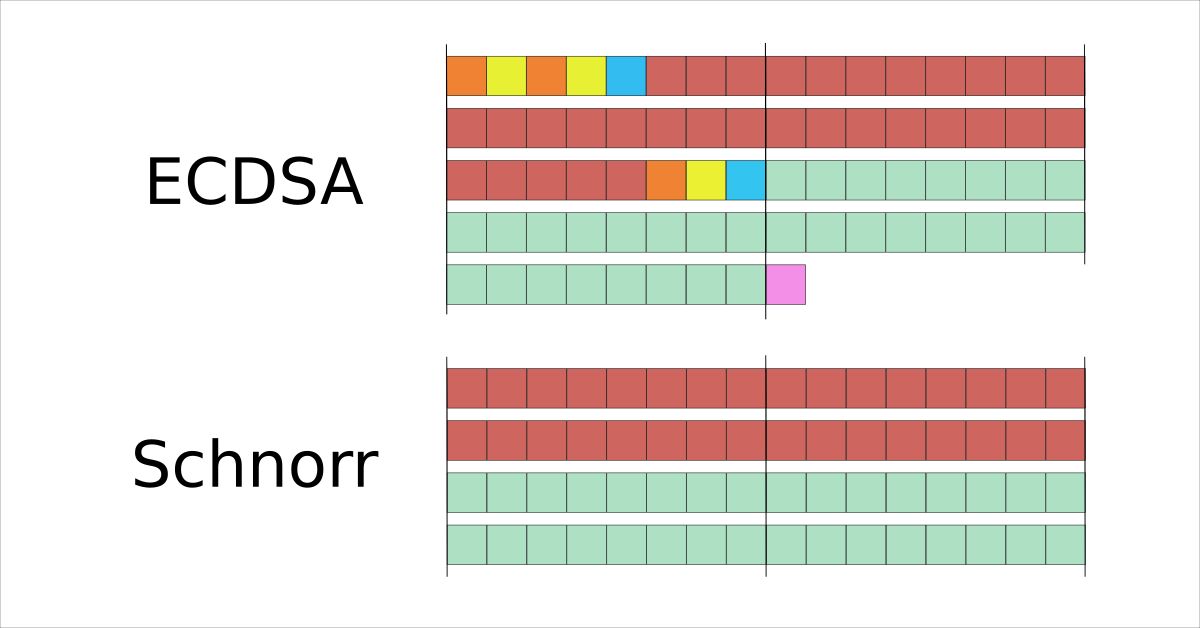
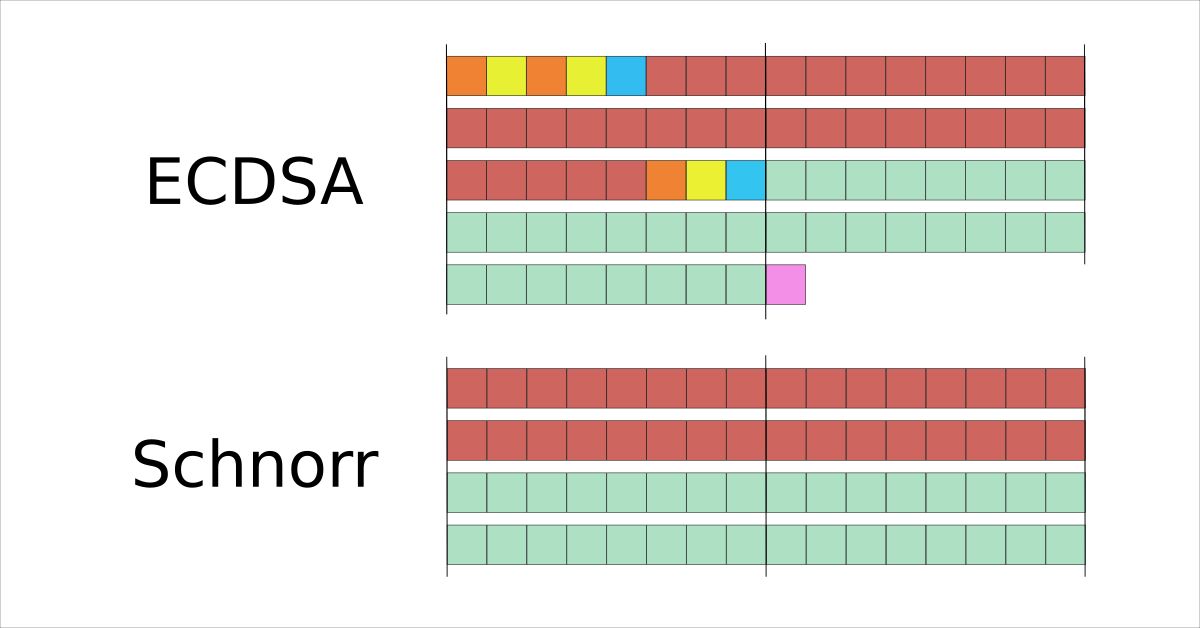 Digital signatures are an essential building block of the Bitcoin protocol and account for a large part of the data stored on the blockchain. We detail how the size of the encoded ECDSA signatures reduced multiple times over the last years and how the proposed Schnorr signature compares to the length of the currently used ECDSA signatures.
Digital signatures are an essential building block of the Bitcoin protocol and account for a large part of the data stored on the blockchain. We detail how the size of the encoded ECDSA signatures reduced multiple times over the last years and how the proposed Schnorr signature compares to the length of the currently used ECDSA signatures.
 Let’s start by understanding about few terminologies and some facts related to this article and come on common ground.
Let’s start by understanding about few terminologies and some facts related to this article and come on common ground.
 SHA-2 (Secure Hash Algorithm 2), of which SHA-256 is a part, is one of the most popular hash algorithms around.
SHA-2 (Secure Hash Algorithm 2), of which SHA-256 is a part, is one of the most popular hash algorithms around.
 The hype is dead, long live the hype. After deep learning, a new entry is about ready to go on stage. The usual journalists are warming up their keyboards for blogs, news feeds, tweets, in one word, hype. This time it’s all about privacy and data confidentiality. The new words, homomorphic encryption.
The hype is dead, long live the hype. After deep learning, a new entry is about ready to go on stage. The usual journalists are warming up their keyboards for blogs, news feeds, tweets, in one word, hype. This time it’s all about privacy and data confidentiality. The new words, homomorphic encryption.
 For decades, we have benefited from modern cryptography to protect our sensitive data during transmission and storage. However, we have never been able to keep the data protected while it is being processed.
For decades, we have benefited from modern cryptography to protect our sensitive data during transmission and storage. However, we have never been able to keep the data protected while it is being processed.
 I once needed to generate a PGP key pair and I thought that I could maybe create my own tool in order to do so.
I once needed to generate a PGP key pair and I thought that I could maybe create my own tool in order to do so.
 XOR is a simple bitwise operation that allows cryptographers to create strong encryption systems.
XOR is a simple bitwise operation that allows cryptographers to create strong encryption systems.
 Randomness is a hard problem for computers. For this reason most functions that generate randomness are not considered cryptographically secure. That means that it is possible that an attacker can take a good guess at what number a non-secure randomness generator generated.
Randomness is a hard problem for computers. For this reason most functions that generate randomness are not considered cryptographically secure. That means that it is possible that an attacker can take a good guess at what number a non-secure randomness generator generated.
 This Slack discussion by Arthur, Limarc, austin and richard-kubina occurred in hackernoon's official #slogging-beta channel. How scared you are of deepfakes?
This Slack discussion by Arthur, Limarc, austin and richard-kubina occurred in hackernoon's official #slogging-beta channel. How scared you are of deepfakes?
 The 5th Cryptoecon Meetup has finished, and it’s time to make a short summary of everything that was discussed there. So far, it was the most interesting meetup among all that we have conducted. Zk-cryptography was discussed and it featured three guests, each of them with his own topic of progressing complexity. We wish to thank RAHIB and CryptoAcademy for the aid in organization!
The 5th Cryptoecon Meetup has finished, and it’s time to make a short summary of everything that was discussed there. So far, it was the most interesting meetup among all that we have conducted. Zk-cryptography was discussed and it featured three guests, each of them with his own topic of progressing complexity. We wish to thank RAHIB and CryptoAcademy for the aid in organization!
 What is a digital signature? It’s probably not what you think it is… in fact, you’re using several right now…
What is a digital signature? It’s probably not what you think it is… in fact, you’re using several right now…
 Quantum cryptography uses physics to develop a cryptosystem completely secure against being compromised without the knowledge of the sender or the receiver of the messages. The word quantum itself refers to the most fundamental behavior of the smallest particles of matter and energy.
Quantum cryptography uses physics to develop a cryptosystem completely secure against being compromised without the knowledge of the sender or the receiver of the messages. The word quantum itself refers to the most fundamental behavior of the smallest particles of matter and energy.
 These stories are from a two-part project. While this part is science fiction, the other part is about reality. Both parts are about mobile, blockchain, and cryptographically secure voting in the context of the US election system. (Reality Piece: link).
These stories are from a two-part project. While this part is science fiction, the other part is about reality. Both parts are about mobile, blockchain, and cryptographically secure voting in the context of the US election system. (Reality Piece: link).
 One of the biggest challenges we netizens encounter is defending freedom and human rights on the internet.
One of the biggest challenges we netizens encounter is defending freedom and human rights on the internet.
 Most interactive Internet applications require a user to first be “registered” in order to use the application and then further require the user to “log on” each time they wish to use the application. This process of first enrolling a user and then later recognizing that user to allow them access may be described as User Authentication. This article focuses on the code and processes used in the registration component of our Authur user authentication system.
Most interactive Internet applications require a user to first be “registered” in order to use the application and then further require the user to “log on” each time they wish to use the application. This process of first enrolling a user and then later recognizing that user to allow them access may be described as User Authentication. This article focuses on the code and processes used in the registration component of our Authur user authentication system.
 That 2020 US Presidential elections would be tight and a nail biter was to be expected. At least by those who had a real feel for American politics
and who took critically the mainstream media propaganda and the sponsored polls for a blue landslide.
That 2020 US Presidential elections would be tight and a nail biter was to be expected. At least by those who had a real feel for American politics
and who took critically the mainstream media propaganda and the sponsored polls for a blue landslide.
 ★ HMAC, a popular authentication mechanism used for authenticating a message using cryptographic hash functions.
★ HMAC, a popular authentication mechanism used for authenticating a message using cryptographic hash functions.
 Repository: entronad/crypto-es
Repository: entronad/crypto-es
 Adi Shamir’s Secret Sharing is a cryptographic algorithm that allows distinct parties to jointly share ownership of a single secret by holding shares
Adi Shamir’s Secret Sharing is a cryptographic algorithm that allows distinct parties to jointly share ownership of a single secret by holding shares
 The Taproot update to Bitcoin will likely be rolled out end of this year, after miners have voted on it. this article will explain why Taproot is a good thing
The Taproot update to Bitcoin will likely be rolled out end of this year, after miners have voted on it. this article will explain why Taproot is a good thing
 In Part 3 of their series on encryption, Chris Hickman and Jon Christensen of Kelsus and Rich Staats of Secret Stache discuss end-to-end encryption in practice.
In Part 3 of their series on encryption, Chris Hickman and Jon Christensen of Kelsus and Rich Staats of Secret Stache discuss end-to-end encryption in practice.
 In the context of public key cryptography, certificates are a way to prove the identity of the owner of a public key.
In the context of public key cryptography, certificates are a way to prove the identity of the owner of a public key.
 Having recently worked with young web developers who were exposed for the first time to proper production infrastructure, I received many questions about the various components that one can find in the architecture of a "Web service". These questions clearly expressed the
confusion (and sometimes the frustration) of developers who understand
how to create endpoints in a high-level language such as Node.js or Python, but were never introduced to the complexity of what happens
between the user's browser and their framework of choice. Most of the
time they don't know why the framework itself is there in the first place.
Having recently worked with young web developers who were exposed for the first time to proper production infrastructure, I received many questions about the various components that one can find in the architecture of a "Web service". These questions clearly expressed the
confusion (and sometimes the frustration) of developers who understand
how to create endpoints in a high-level language such as Node.js or Python, but were never introduced to the complexity of what happens
between the user's browser and their framework of choice. Most of the
time they don't know why the framework itself is there in the first place.
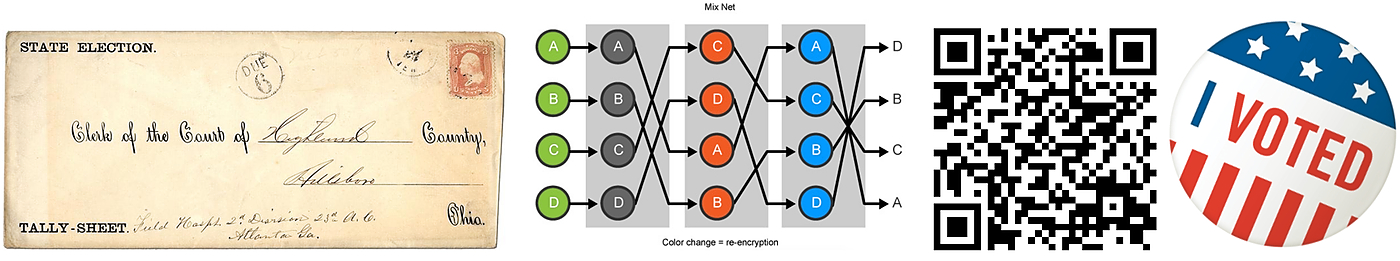 This is a two-part project. This part is about reality. The other part is science fiction. Both are about mobile, blockchain, and cryptographically secure voting systems in the context of US elections. (Science Fiction: link)
This is a two-part project. This part is about reality. The other part is science fiction. Both are about mobile, blockchain, and cryptographically secure voting systems in the context of US elections. (Science Fiction: link)